Getting Started with Purple Teaming and Adversary Emulation
A collection of resources for adversary emulation and purple teaming
Why Purple Teaming?
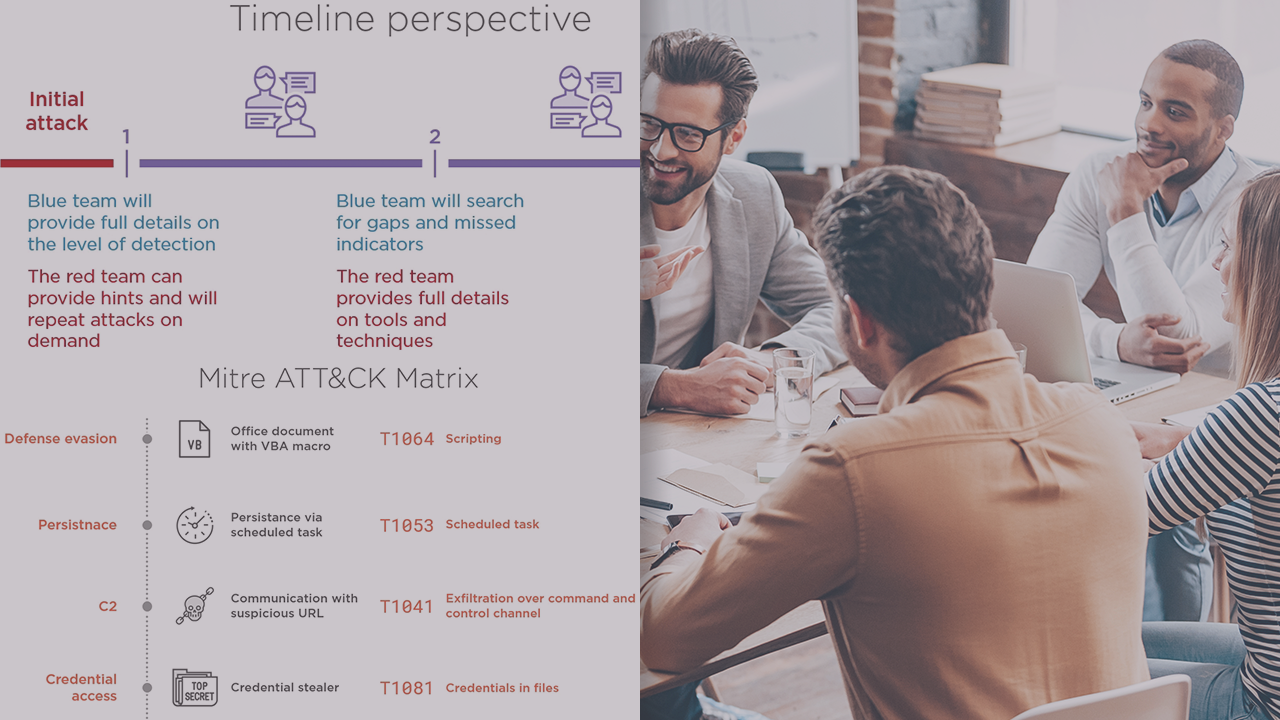
Purple teaming is a new trend in the information security industry that comes as an evolution to existing red team and penetration testing exercises. It infers that defenders go beyond monitoring alerts, and actually understand and disect adversary techniques, tactics and procedures. Rather than pitting red team against defenders, a.k.a blue team, purple teaming aims at the collaboration between the two teams to go into a much grater level of visibility and detection.
I personally think purple teaming adds a lot of value not only to defenders but also offensive professionals as well. I have put together a course that provides insight into how to migrate to a pruple team mindset and how to get more value out of the current efforts and capabilities.
If you don't have a Pluralsight account, but would still like to view my course, you can sign up for a free trial at this address: https://pluralsight.pxf.io/yDPX3
Resources for adversary emulation
Not so long ago, if someone wanted to recreate or simulate a cyber attack or part of it, the only option was to use the same tools and exploits that were used in the actual attack. Well, now we have more options which provide us all the capabilities to simulate advanced techniques without having to deal with live malware or exploits. This category of tools is called adversary emulation tools, and there are a few out there that fit the needs of large and small organisations. These set of tool are very suited to test the effectiveness of security controls, such as EDR, NGFW, AV etc. against offensive techniques. This goes into the realm of behavioral analysis over traditional signature-based analysis.
- Caldera: https://www.mitre.org/research/technology-transfer/open-source-software/caldera™
- Red Team Automation (RTA) scripts: https://www.elastic.co/blog/introducing-endgame-red-team-automation
- Atomic Red Team: https://atomicredteam.io
Maybe one important note is not to experiment with these tools directly on production, you can set up this in a lab environment or with test machines.
Incident simulations
While adversary emulation tools are a great way to assess the efficienty of detection capabilities, another important part of incident handling are the playbooks and processes to ensure defenders efficiently triage between false positives or commodity malware and hidden threats that might go below the radar. This is where tabletop exercises come into play
- https://www.cisecurity.org/white-papers/six-tabletop-exercises-prepare-cybersecurity-team/
- https://www.mitre.org/publications/technical-papers/cyber-exercise-playbook
More interesting articles on this topic
- https://www.redscan.com/news/purple-teaming-can-strengthen-cyber-security/
- https://www.tripwire.com/state-of-security/risk-based-security-for-executives/connecting-security-to-the-business/top-4-tips-for-purple-team-exercises/
- https://securitytrails.com/blog/purple-team
- https://danielmiessler.com/study/purple-team/
- https://danielmiessler.com/study/red-blue-purple-teams/

